Blog
-
Cybersecurity: What Should Banks Prioritize First for 2019? [VIDEO]
{{ script_embed(‘wistia’, ‘j9j3ai6oqc’, ”, ‘inline,responsive’) }} (more…) -
Social Engineering
Social engineering is a collection of techniques used to manipulate people into performing actions or divulging confidential information. Some people also call it ‘human hacking’. The term typically applies to trickery for information gathering or computer system access.
-
Good reminder for Vendor Risk Management

Although this article in Consumer Compliance Outlook is a little dated, it comes as a good reminder regarding your vendor risk management. Over the last couple of years we have noticed a continued effort by examiners to increase their own due diligence towards financial institution’s understanding and management of their vendor programs. A direct quote that stands out to me is….
(more…) -
Wearables in Health Care: How to Ensure Cloud Information Security
As you must with any new technology, your health-care practice needs to consider information security issues when moving to wearable health-care monitors.
(more…) -
RISK: It’s Everyone’s Business
Recently IBM released its 2010 Global IT Risk Study. According to the study 74% of those surveyed agreed that the greatest benefit of improving IT Risk Management is that it ensures business continuity.
(more…) -
4 Essentials Every Company Needs for an Incident Response Plan
Behind nearly every cybersecurity breach in recent years is a business or organization that was left to grapple with the fallout. Indeed, organizations that suffer a major security incident can end up spending tens, or even hundreds of millions of dollars on remediation costs, fines, damages and other related expenses.
However, even major breaches can be dealt with effectively when the affected organization has a formal incident response plan, making it one of your most important risk management solutions. Here are four key components of every good incident response plan. -
What Do The Worst Passwords of 2015 Say About Us?
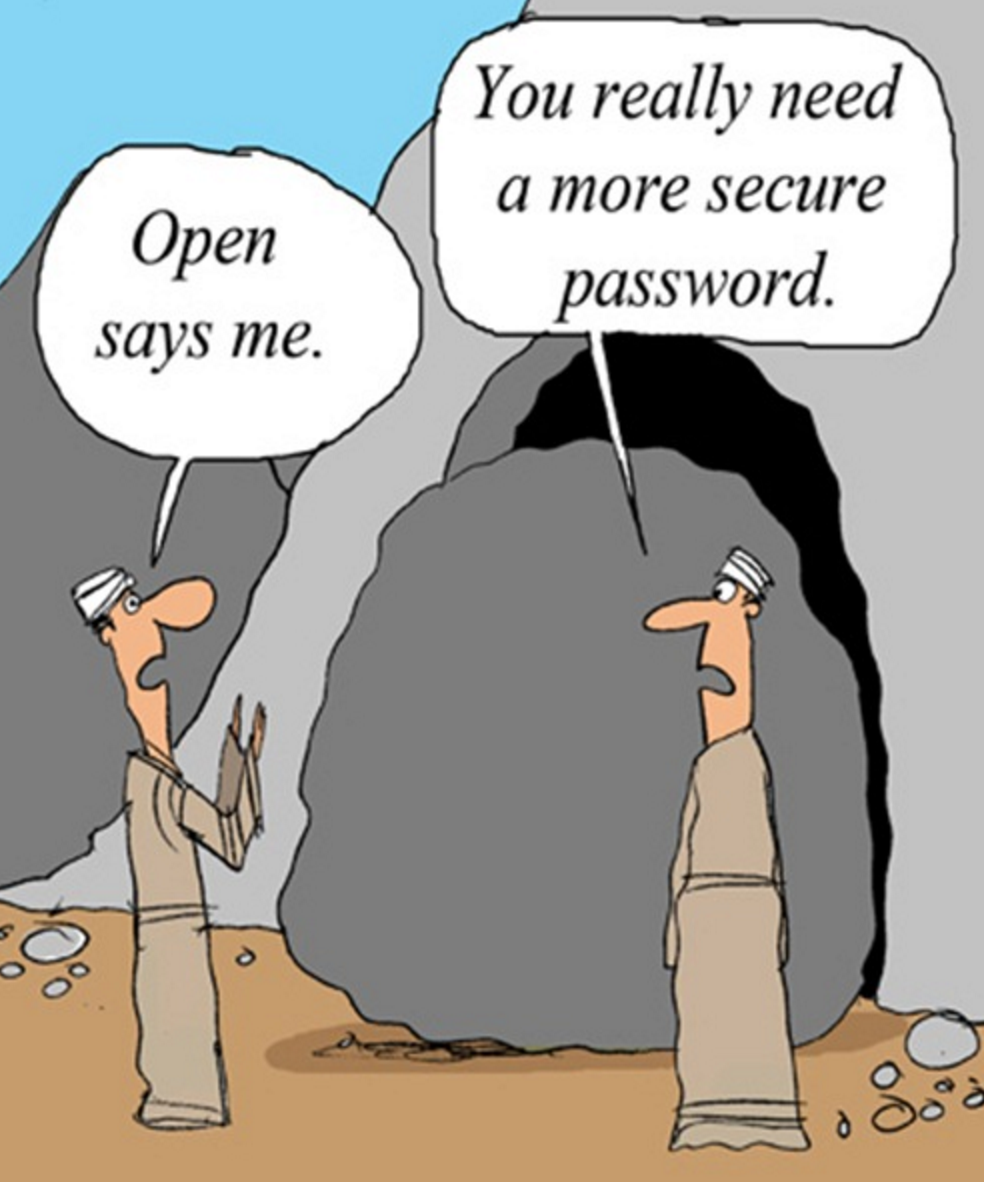 In the 2015 edition of its annual worst passwords list, password management company SplashData revealed the 25 most common (and most easily compromised) passwords for the year. Based on an analysis of more than 2 million passwords revealed through searches of publicly available plain text data dumps, the report found that the Internet public is still clinging to its bad password habits.
In the 2015 edition of its annual worst passwords list, password management company SplashData revealed the 25 most common (and most easily compromised) passwords for the year. Based on an analysis of more than 2 million passwords revealed through searches of publicly available plain text data dumps, the report found that the Internet public is still clinging to its bad password habits. -
Staying Secure & Safe This Holiday Season
(more…) As most of us are frantically running around to find the last minute gifts for family and friends, we seldom think about security. Most of us trust the places we shop and assume they have all the latest and greatest sure payment methods. Here are a few ways to stay safe when shopping online and in store this holiday season.
As most of us are frantically running around to find the last minute gifts for family and friends, we seldom think about security. Most of us trust the places we shop and assume they have all the latest and greatest sure payment methods. Here are a few ways to stay safe when shopping online and in store this holiday season.

