Do you fear you don’t have the talent or funds to be able to keep your business secure? Is your IT person maxed out on projects that adding infosec to her plate might be too much? How can you find the balance between getting the cybersecurity expertise your business requires while not breaking the bank?
The Information Security space has become a multi-billion dollar industry and has a wide range of diverse jobs within it. Whether someone goes down the development path, the testing/forensics path, or even the strategic path there is much opportunity and it’s extremely competitive retaining people. Cybersecurity Ventures predicts there will be 3.5 million cybersecurity job openings by 2021. Additionally, just because you get someone to fill the role also doesn’t mean 1) They have the skillset to accomplish everything you need or 2) be a strong culture fit that can get their heads out of the technical weeds and talk to you in the business terms you need.
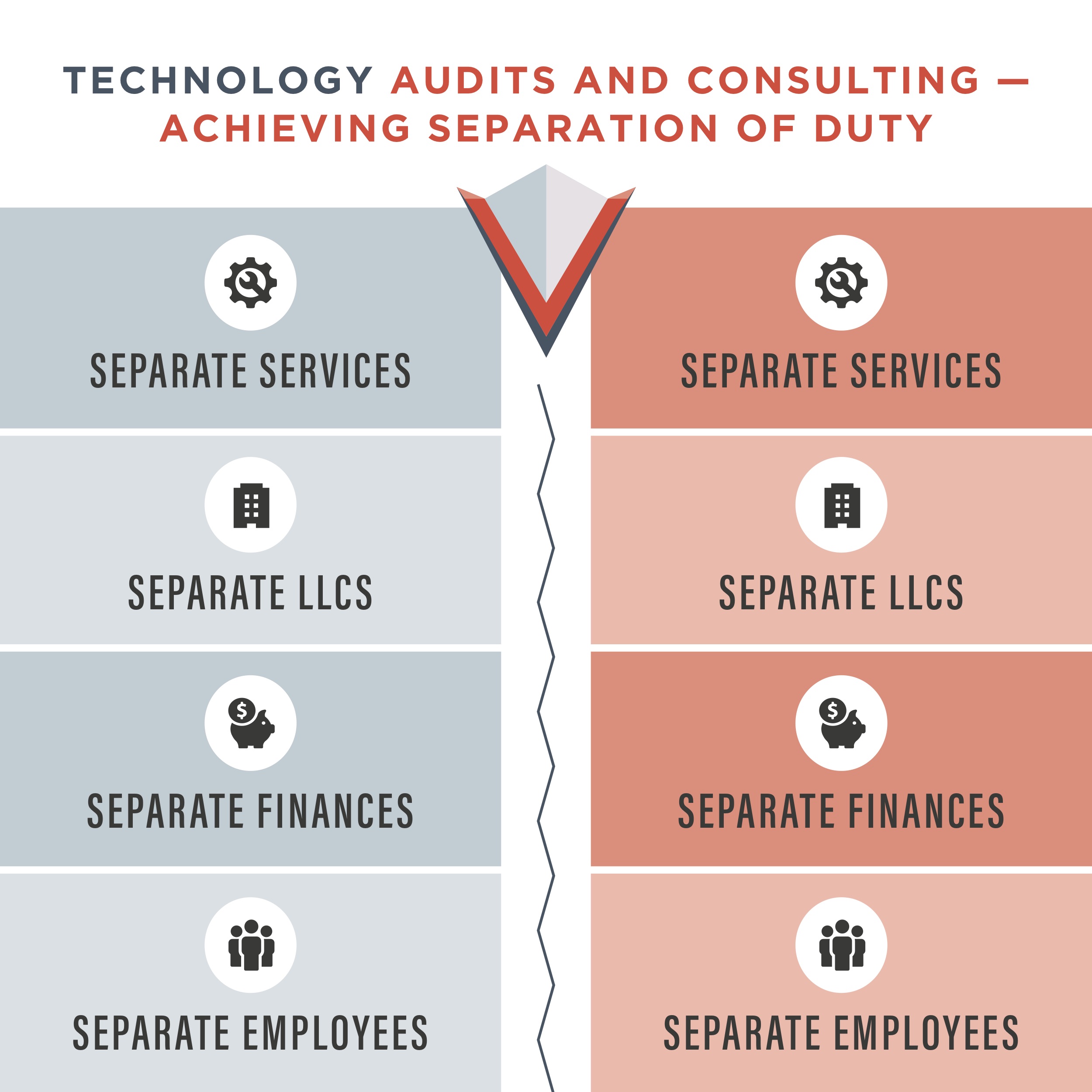
Often fulfilling those needs can be done in an outsourced way. You have a great Technology audit experience or a great relationship with a fractionalized Information Security Officer that is able to align all the technical projects into the business strategic plans or even better, both! But wait, isn’t that a conflict of interest? Having auditors and ISOs from the same company? At quick glance, I could see why one would think that. But, if managed properly, we believe you could have an even better experience by utilizing one company for both. Here are some of things you can plan for to ensure achieving good separation of duty.
- State What You Wanted to Happen
- Acknowledge What Actually Happened
- Lessons Learned from the Experience
- Adjust Your Behavior
We love this tool as it focuses on the right things with the right mindset. Instead of it becoming a blow-out debate on who’s right and who’s wrong it instead becomes a collaborative, incremental improvement discussion on stating what happened and what can we do next time to improve upon that experience. We highly recommend trying it out!
In summary, in this competitive cybersecurity world strong, outsourced relationships are hard to find. Businesses should look for ways to leverage their strongest relationships and not get stuck with dealing with a ‘lesser choice’ just because of concerns around separation of duty. You can bring it together and with a little planning (and after action reviews) you can be successful together.
FAQs on How to Achieve Proper Separation of Duty
Why is it better for you to work with one company to do both IT audits and consulting?
Working with an extra vendor adds more conversations, more contractual frustration, and the focus being on vendor relationships instead of where it can be which is making your organization secure.
What would the obstacle be if you want to work with a company who does both?
At Vala Secure there is no obstacle. There is no legal requirement to use separate companies. Our clients understand our processes and have been successful in passing exams and adding regulated clients.

 Negotiating vendor contracts is never easy. You need strong relationships with your vendors to grow and expand your business, but rushing to sign on with companies may lead to higher risk deals. Your short-term needs may get met, but you suffer over the long-term from it. If you do not have the technology and relationship to scale effectively and securely while maintaining compliance you may not be able to keep up with your competition and customer/client demands.
Negotiating vendor contracts is never easy. You need strong relationships with your vendors to grow and expand your business, but rushing to sign on with companies may lead to higher risk deals. Your short-term needs may get met, but you suffer over the long-term from it. If you do not have the technology and relationship to scale effectively and securely while maintaining compliance you may not be able to keep up with your competition and customer/client demands.


 It’s no secret that 2015 was another challenging year in cyber security. While fallout continued from the Sony hack, new threats emerged and each one offered a lesson for the future. Here’s what can be learned from the past year as you
It’s no secret that 2015 was another challenging year in cyber security. While fallout continued from the Sony hack, new threats emerged and each one offered a lesson for the future. Here’s what can be learned from the past year as you 